THE END OF THE ANNUAL PENTEST
Why Continuous Security Validation Is the New Standard for Enterprise Defense 95% of enterprises rank penetration testing as a top priority—yet they test only 32% of their attack surface. Exploits now emerge within hours of disclosure, not weeks. The annual...
What a Pentest Actually Covers And… What It Does Not
Scoping, rules of engagement, and the real difference between pentesting, vulnerability scanning, and red teaming. Note: All screenshots in this article are illustrative examples built from fictional data. They are included to show what good scope, rules of engagement, and...
The clock is running out — and pentesting is no longer optional
Attackers used to give you a month to patch. Now they give you five days. Meanwhile, regulators are giving organizations no choice but to test — or face the consequences. Here’s a belief that still lives in a lot of...
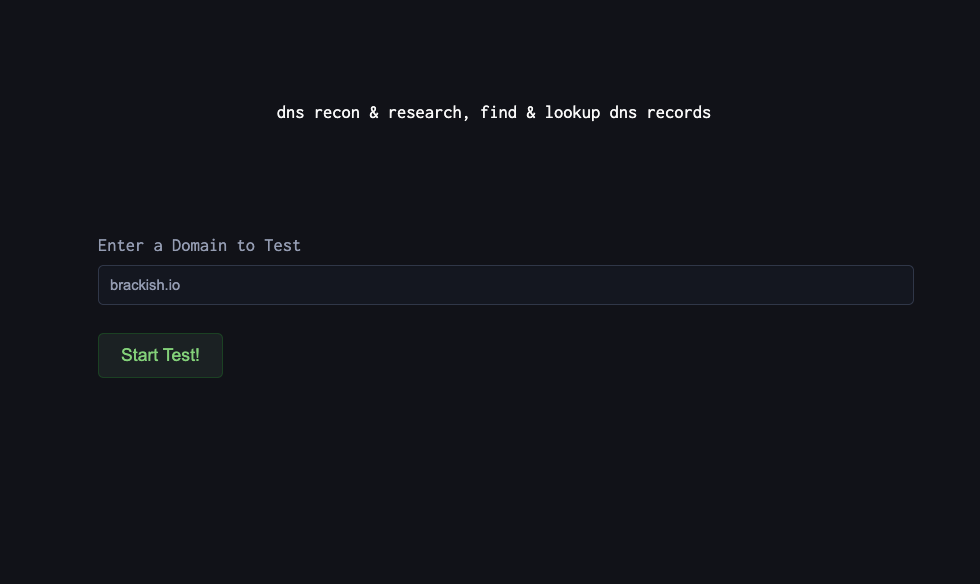
DNS Reconnaissance for Defenders: Using DNSDumpster to Map Your External Attack Surface
Before we go on. What is DNS Dumpster? DNSDumpster is a free, web-based reconnaissance tool that collects and visualizes publicly available DNS information about a domain. Instead of manually querying DNS records or running multiple tools, DNSDumpster aggregates data like:...
The Expanding Attack Surface: Why Visibility Alone is Not Security
Organizations today have more visibility than ever before. Dashboards enumerate assets. Cloud inventories track deployments. External attack surface management tools identify exposed services. Continuous monitoring platforms scan for misconfigurations. On paper, visibility has improved dramatically. Yet breaches continue to originate...
Security vs Compliance: Why Passing an Audit Isn’t the Same as Being Secure
Many organizations believe they are secure because they are compliant. They pass SOC 2 audits. They maintain ISO certifications. They satisfy HIPAA, PCI, or regulatory requirements. Policies are documented. Controls are implemented. Risk assessments are filed. On paper, everything appears...
When “Low Severity” Becomes High Impact: The Limits of Vulnerability Risk Management
Security teams triage vulnerabilities every day. Findings are categorized. Severity is assigned. Remediation timelines are scheduled. Dashboards reflect progress. The process appears disciplined. Yet some of the most damaging breaches in recent years began with vulnerabilities that were not initially...
The 5 Things to Do This Quarter to Prepare for 2026 Cyber Threats
Stop trying to predict the next headline. Start removing the easiest paths in. If 2026 is teaching security leaders anything, it’s this: the most damaging cyber incidents aren’t always “loud.” Many are quiet, patient, and designed for leverage—long-term access, disruption...
Top External Network Penetration Testing Findings of 2025
With 2025 in the bag, we wanted to start an annual series highlighting the top findings from the previous year. As trends and technology shifts, as will these findings. We will start with external and dive into internal & web...
AI Changed the Rules: The Threats You Need to Model in 2026
AI is no longer an “innovation project.” In 2026, it’s embedded in how teams hire, support customers, review transactions, manage access, and make decisions at speed. That’s the opportunity and the problem. When you put AI into production, you don’t...