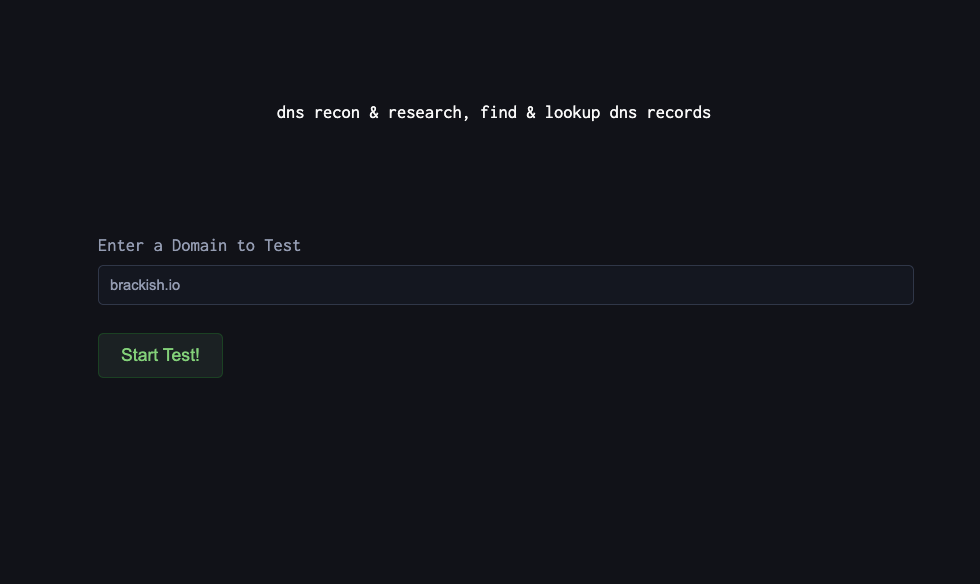
DNS Reconnaissance for Defenders: Using DNSDumpster to Map Your External Attack Surface
Before we go on. What is DNS Dumpster? DNSDumpster is a free, web-based reconnaissance tool that collects and visualizes publicly available DNS information about a domain. Instead of manually querying DNS records or running multiple tools, DNSDumpster aggregates data like:...
CVSS v4 vs CVSS 3.1 – What’s New and Improved
Recently an update to CVSS scoring was released – CVSS V4. But, the real question is why was an update needed? What was wrong with CVSS 3.1? A few things were wrong. Amongst them are: What does v4 now do...
External Penetration Testing in 2026: Why Proactive Security Matters More Than Ever
As we move into 2026, an organization’s external-facing assets remain the most targeted—and most tested—entry points for cyber attackers. Websites, web applications, APIs, cloud infrastructure, and public-facing services continue to expand, often faster than security teams can fully account for....
TSA’s Proposed Cybersecurity Rule for the Transportation Sector – The Need for Penetration Testing
In an era where cyber threats are increasingly sophisticated, the Transportation Security Administration (TSA) has proposed a new set of cybersecurity requirements targeting the pipeline, rail, and over-the-road bus (OTRB) sectors. This Notice of Proposed Rulemaking (NPRM) aims to strengthen...
Web and Mobile Application Fuzzing Best Practices
If you’re reading this, you’ve probably used tools like Ffuf or Gobuster to fuzz an application to expand the attack surface and potentially find sensitive files and directories. Unfortunately, we here at Brackish find that a lot of testers are...
JavaScript Source Map Vulnerabilities
What is a JavaScript source map file? Source map files map the transformed, minified, or compiled code back to the original source code, and they can often be found exposed publicly in web applications. This is particularly useful for debugging...
IoT Penetration Testing Part 1
IoT Penetration Testing is one of our favorite types of testing here at Brackish Security. This will be the first of a multi-part blog series on embedded device security (the “Internet of Things” or IoT). Our goal is to show...
Tales from Pen Testing Trenches: MAC Address Whitelisting Failure
MAC address whitelisting is commonly perceived as a foolproof network security mechanism. Yet, Brackish Security’s recent test on a wireless network illustrates how easily this method can be bypassed, challenging its efficacy as a standalone security solution. MAC address whitelisting...
What is Blind XSS?
You may have heard of Reflected Cross Site Scripting (XSS) or Stored XSS, but what is Blind XSS? Unlike traditional XSS attacks, where the immediate impact is visible, Blind XSS vulnerabilities are typically triggered when the malicious input is viewed...
Shodan Series Part 2: The Untraditional Web Ports
Our goal of this series is to revisit Shodan and demonstrate to IT admins and business owners, how much an attacker can glean of a network without sending any packets to the actual to an organization. Our last post focused...