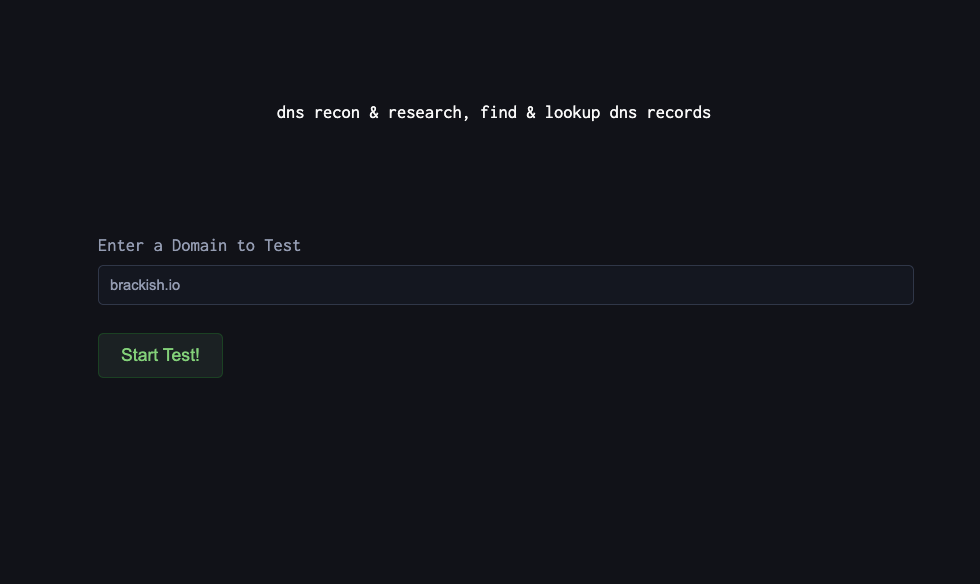
DNS Reconnaissance for Defenders: Using DNSDumpster to Map Your External Attack Surface
Before we go on. What is DNS Dumpster? DNSDumpster is a free, web-based reconnaissance tool that collects and visualizes publicly available DNS information about a domain. Instead of manually querying DNS records or running multiple tools, DNSDumpster aggregates data like:...
The Expanding Attack Surface: Why Visibility Alone is Not Security
Organizations today have more visibility than ever before. Dashboards enumerate assets. Cloud inventories track deployments. External attack surface management tools identify exposed services. Continuous monitoring platforms scan for misconfigurations. On paper, visibility has improved dramatically. Yet breaches continue to originate...
Security vs Compliance: Why Passing an Audit Isn’t the Same as Being Secure
Many organizations believe they are secure because they are compliant. They pass SOC 2 audits. They maintain ISO certifications. They satisfy HIPAA, PCI, or regulatory requirements. Policies are documented. Controls are implemented. Risk assessments are filed. On paper, everything appears...
When “Low Severity” Becomes High Impact: The Limits of Vulnerability Risk Management
Security teams triage vulnerabilities every day. Findings are categorized. Severity is assigned. Remediation timelines are scheduled. Dashboards reflect progress. The process appears disciplined. Yet some of the most damaging breaches in recent years began with vulnerabilities that were not initially...
CVSS v4 vs CVSS 3.1 – What’s New and Improved
Recently an update to CVSS scoring was released – CVSS V4. But, the real question is why was an update needed? What was wrong with CVSS 3.1? A few things were wrong. Amongst them are: What does v4 now do...
The 5 Things to Do This Quarter to Prepare for 2026 Cyber Threats
Stop trying to predict the next headline. Start removing the easiest paths in. If 2026 is teaching security leaders anything, it’s this: the most damaging cyber incidents aren’t always “loud.” Many are quiet, patient, and designed for leverage—long-term access, disruption...
Top External Network Penetration Testing Findings of 2025
With 2025 in the bag, we wanted to start an annual series highlighting the top findings from the previous year. As trends and technology shifts, as will these findings. We will start with external and dive into internal & web...
AI Changed the Rules: The Threats You Need to Model in 2026
AI is no longer an “innovation project.” In 2026, it’s embedded in how teams hire, support customers, review transactions, manage access, and make decisions at speed. That’s the opportunity and the problem. When you put AI into production, you don’t...
OWASP Top Ten 2025
The OWASP Top Ten is one of the most influential security awareness documents in application security, published by the Open Worldwide Application Security Project (OWASP). It represents a community-driven ranking of the most critical risks facing web applications. The 2025...
External Penetration Testing in 2026: Why Proactive Security Matters More Than Ever
As we move into 2026, an organization’s external-facing assets remain the most targeted—and most tested—entry points for cyber attackers. Websites, web applications, APIs, cloud infrastructure, and public-facing services continue to expand, often faster than security teams can fully account for....